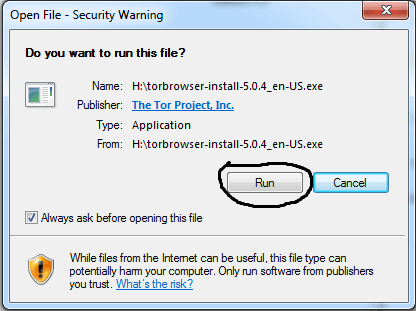
While Tor Browser provides a degree of anonymity, accessing the dark web inherently involves exposure to a multitude of potential dangers. Unknown or suspicious links should be avoided as they may lead to harmful content, phishing sites, or malware. As discussed earlier, configuring Tor Browser’s security level is paramount for safer browsing on the dark web.
Choose A VPN That’s Good For Accessing The Dark Web
Research what they offer and assess your privacy needs to make a decision about which dark web browser works best for you. While both tools enhance online privacy, they work differently. When using Tor, practice good security hygiene by avoiding suspicious links and using reliable antivirus software.
Why Abandoned Domain Names Are So Dangerous
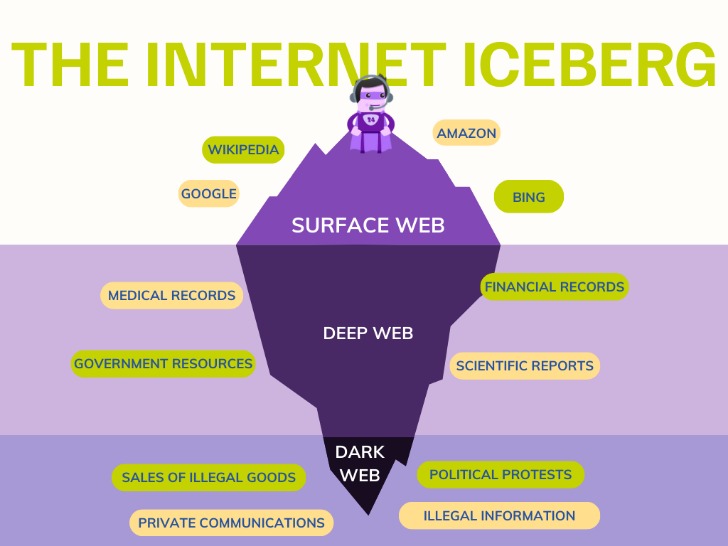
As I mentioned above, the dark web is a decentralized, non-indexed network of web pages, and the sites don't use standard URLs. Deep web content includes academic research papers, court documents, or medical records. That’s why I’m not going to provide links or detailed instructions for accessing the internet’s shadier side. Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity's sake. Darknet browsers provide access to the dark web and allow for anonymous browsing. Users need to be cautious about the websites they visit and the files they download.
Https://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqdonion/
Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online. By using a VPN to connect to Tor — a special browser designed to access the dark web — you can securely access the dark web using a technique known as Tor-over-VPN. Finally, it lets you appear as if you’re browsing from a specific country (the country the VPN server you’re connected to is in). VPN over Tor means you connect to the Tor network first, and then your traffic goes through a VPN. As long as you avoid engaging with illegal content, you have nothing to worry about.
- Unlike the clear web, where websites are often rated or reviewed, most dark web sites are unregulated.
- The desire of intelligence services to de-anonymize Tor users highlights the necessity of taking strict security measures.
- Threat actors also exploit vulnerabilities in your systems and software to gain access to them.
- When used in unison, these tools seal the security and privacy vulnerabilities of the Tor network, keeping you anonymous as you roam the streets of the dark web.
- Gannicus Oliver is an experienced tech journalist (he loves writing on emerging techs and digital privacy issues) and an online business consultant.
The Hidden Wiki & Co
Deep web websites are the pages behind paywalls, authentication forms, logins, and passwords. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. Look for unusual domain formats, misleading content, and always cross-check onion addresses. Use VPN, avoid logging into personal accounts, enable Tor security settings, and stick to trusted sites.
You might’ve heard of the domain extension called “.onion“, which sits at the end of each dark web website. You can go on the dark web safely, use legal sites, and enjoy the experience without worries. Relying on Tor to keep you anonymous online is a good recipe for disaster; you’ll learn why. We know what you’re thinking, or some of you. The so-called surface web is readily accessible to all of us and less interesting. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures.
Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic. After installation, you can use Tor to access the public internet as well as .onion websites. After your data is secured inside multiple layers of encryption, your web traffic is transmitted through a series of network nodes, called onion routers. Powerful antivirus software with advanced Dark Web Monitoring Features like Norton 360 Deluxe can help keep your internet browsing private and secure. Only about 6.7% of global users use the dark web for malicious purposes, but it’s smart to be selective about the websites you access. Tor Browser gives you access to .onion websites that are available only within the Tor network.
As a result, users often rely on specialized search engines specifically designed to discover onion services. Unlike the surface web, where search engines like Google and Bing index vast amounts of content, onion services are generally not indexed by traditional search engines. These services utilize unique web addresses ending with the .onion top-level domain, signifying that they are accessible only through the Tor network. While this may cause some websites to lose certain functionalities, the enhanced security is often considered a worthwhile trade-off, especially when navigating potentially risky parts of the internet.
Dark Web Access Guide: How To Enter The Dark Web Safely

A bridge creates an obfuscated relay on the Tor network that is not listed in the main directory. One of the major advantages of using Tor in overly-restrictive countries is that it keeps your online travels private. That said, the Tor Browser and a VPN make an excellent team for protecting your online activities from prying eyes, and provide optimal online privacy protection. This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities.

Use A Quality VPN
From cybersecurity researchers to IT managers, understanding how to navigate the dark web can help monitor cyber threats, protect sensitive data, and investigate cybersecurity incidents. Some governments actively monitor or block Tor traffic, and Tor use can raise suspicion even when not used for illegal activities. In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts. Websites often install trackers to monitor your activities, including those on other websites.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
The purpose of Tor is to remain anonymous, and entering any personal information online could comprise it. And make sure your network’s protected by a firewall and the best antivirus software. Knowing how to safely use Tor means using it alongside other cybersecurity tools, so set up a VPN to benefit from end-to-end encryption. Your government may also track your activities if you use Tor. ISPs have been known to throttle internet speeds and even contact customers about Tor usage. Using Tor can call undue attention to your web activity, which is counter-productive if you’re seeking privacy.
Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. Take a look at the sites that these directories have collected and see what topics interest you. Do not explore random links to websites you aren't aware of or familiar with. Only visit trusted websites with URLs that are maintained by a trusted source.
You can still be tracked at network entry and exit nodes, as indicated by reports that police identified Tor users by surveilling data centers. The deep web is the next layer, and it encompasses a massive amount of online data that is not available for public consumption and not indexed by clear web search engines. The clear web is made up of websites that you can get to via a search engine like Ecosia or Google. There’s also little to no recourse to be had if you encounter any trouble there, because the dark web is a decentralized collection of websites hidden from search engines. Yes, darknet browsers like Tor facilitate access to regular internet sites.
- Accessing the dark web is legal in India as long as you do not engage in illegal activities such as buying drugs or hacking services.
- Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they're doing and what they're looking for.
- If you’re one of them, good luck finding a provider that supports it.
- Not very safe, but it’s still useable.
- Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing.
As in the real world, the price you pay for stolen data fluctuates as the market changes. The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences. The inherent anonymity of the place attracts scammers and thieves, but what do you expect when buying guns or drugs is your objective? “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet.
How To Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL
You can never be sure of the motive of the person operating the node that your traffic is routed through. Regardless of what brings you to the dark web, you should be aware of the dangers emanating from the limitations of the Tor network. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons. However, using the dark web for illegal activity can be a criminal offense.



