Balancing these trade-offs with robust security ensures safe, ethical exploration. These experiences taught me to use Tails OS, verify links, and stick to filtered engines for sensitive work. A 2023 Torch search accidentally led to a questionable forum, which I exited immediately. OnionLand’s JavaScript reliance risks this; I disable it after a 2025 warning on r/onions. A 2023 Torch search for “crypto forum” surfaced a drug marketplace, which I immediately exited. I used NotEvil to find a censored news aggregator in 2025 for a media piece.
The lack of filtering means I’m always on guard, cross-checking links with Torlinks or r/onions. In another test, I searched for I2P content (“I2P forum”), but results were sparse, and I switched to a dedicated I2P tool. However, its reliance on JavaScript for full functionality raises privacy concerns, as enabling it can expose users to tracking or deanonymization. However, its smaller index frustrates me when casting a wider net, and the lack of robust filtering means I still verify links via tor.taxi. In another instance, I used DeepSearch’s API to scrape a cybersecurity blog for a report, and its clean data saved hours of manual filtering.
Formerly known as Archive.is, it is one of the best onion sites on the dark web. The downside is that it limits data to only 25mbps per user. Using the ProtonMail .onion site offers security and privacy advantages. Furthermore, data will help to detect attacks against the network and possible censorship events.
Ransomware Threat Actors
Default Tor Browser search engine offering private search without tracking, accessible via .onion URL. With it's unparalleled speed, vast index and advanced filters for fine grained results nothing comes close to this tor dark web search engine Plus, dark web search engines can also allow political dissidents to bypass government censorship, or for journalists to safely engage with whistleblowers. The Tor browser, short for The Onion Router, is software that allows users to access the Tor network. Ransomware threat actors use malware to lock users out of their systems, demanding payment to restore access. The dark web is a portion of the Internet that is inaccessible to normal search engines.
WordPress 69 Roadmap – Expected Release Date & Features
DuckDuckGo is a privacy focused search engine that you can use on the dark web via its Tor hidden service onion address. To reach the dark web, you must use Tor and then a dark web search engine or directory to find addresses. We’ve covered how tools like Ahmia and DuckDuckGo’s onion service keep things clean and private, while veterans like Torch and Haystak offer deep access with caution. To sum up, dark web search engines are a valuable extension of the professional hacker toolkit.
Security Links
It catalogs about 1.5 billion pages, encompassing over 260,000 websites, making it a resourceful engine. Our Dark Web API crawls the deep and dark web, providing structured feeds of illicit content kept locked away with encryption and password protection. Known for its efficient indexing and unique features, Tor66 stands out as a valuable tool for users seeking to explore the dark web. It offers a straightforward interface and a range of features, making it an appealing choice for users seeking to explore the dark web. A responsive support system and active community engagement can significantly enhance the reliability and usability of a search engine. It is a hub for black markets where criminals trade illegal goods and services, such as drugs, weapons, counterfeit currency, and stolen data.
WooCommerce Version History – Latest Releases & Future Scenario
- It has become a useful research tool for law enforcement, researchers, and those simply curious about the dark web economy.
- While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.
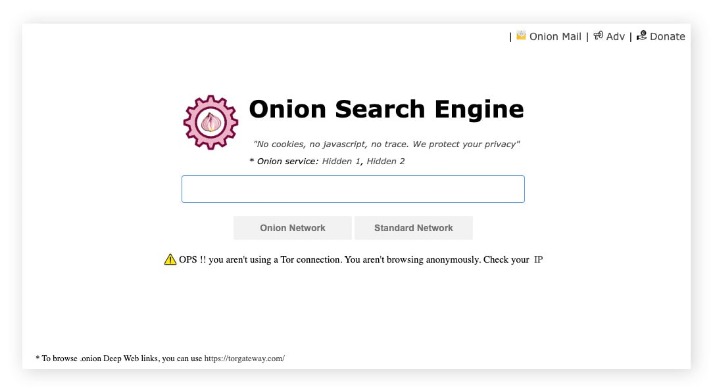
- So-called “onion sites” are only accessible via special network configurations or browsers like Tor that can connect you to .onion domains via onion routing.
- The lack of standardization and numerous malicious sites further complicate navigation.
- You will need the Tor browser to access these links and the other (hidden) internet, the dark web.
It’s one of the simplest deep web search engines that exists, and because it’s similar to Google on its interface you won’t find using it hard either. In this list of the Dark web search engines, I’ll list some search engines and sites or webpages which have a long list of deep/dark web sites. Because the deep/dark web isn’t available on the conventional search engines, you can’t find sites for the same on Google/Yahoo or Bing.
Some Of The Big Things On The Hidden Wiki You Should Know

I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. This means your activities cannot be traced or your browser history exposed. Since the internet is open to everyone, there is no privacy. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. For example, you can find information unavailable to the public and share data privately while protecting your online identity. However, you can find legitimate content and activities here, too.
Torch: One Of The Oldest Dark Web Search Engines
The dark web's anonymity is one of its primary security features, and violating it can make you a target for identity theft or phishing. Outdated software may contain vulnerabilities that allow exploits to bypass the online anonymity provided by the Tor network. It is a tool for searching the regular internet, but anonymously. It is critical to note, however, that DuckDuckGo is a surface web search engine. The engine's primary focus is on delivering reliable results and helping users avoid danger.
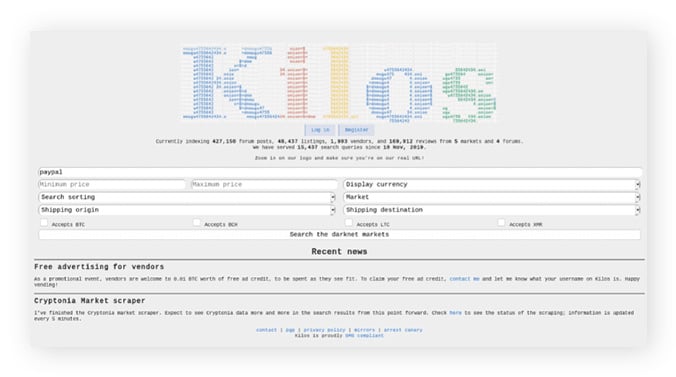
Kilos is a dark web marketplace search engine that lets users search for specific products they’re looking for. It’s technically not a dark web search engine but is still a useful tool to navigate the dark web and find sites more easily based on categories. Haystak is one of the most comprehensive dark web search engines, with a search library of more than 1.5 billion pages. And many people use a VPN with Tor, because while the Tor network offers anonymity and privacy, extra security is recommended when accessing the dark web. These websites live on the unindexed, hidden part of the internet known as the dark web.
The dark web refers to encrypted online content not indexed by traditional search engines like Google or Bing. In this comprehensive guide, we’ll introduce the top dark web search engines in 2025, their features, and how to use them securely. This applies to users whose raw genotype data or health predisposition reports were accessed. Between April and September 2023, hackers conducted a credential stuffing attack—using stolen usernames and passwords from other breached websites to access 23andMe accounts.

Additional Features
The Ahmia search engine offers users an uncensored search experience. Yet, it helps users explore the open model and user-driven content, enabling them to unearth a broader range of dark web sites. Additionally, the search engine helps index a wide range of .onion links and offers a premium version. Haystak is also a renowned unfiltered web search engine that provides users with an uncensored yet privacy-focused search experience. Regarding dark search engines, they are designed to index all content on the dark web. Unsurprisingly, these unfiltered engines largely depend on the Tor network, which is not the case with leading formal search engines such as Bing, Google, and Yahoo.
A safer way to search and browse online without personal data collection, tracking or targeting. The world’s most private search engine. The dark search engine is a one-stop shop for cybercriminals, hackers, and other cyberterrorists. Moreover, it mainly comprises usual sites that require visitors to create accounts before they can visit them.
Use default bridges or consult torproject.org for custom setups in censored regions. However, privacy risks (e.g., AI tracking, regulatory overreach) demand vigilance. By 2030, ethical debates over content moderation could split the ecosystem, with some engines (e.g., Torch) remaining unfiltered and others (e.g., NotEvil) adopting stricter policies. NotEvil’s community-driven ethos aligns with this trend, though adoption hinges on user trust and technical maturity. By 2030, blockchain-based indexing could create tamper-proof, community-driven .onion catalogs, aligning with NotEvil’s non-profit model.
When not dissecting .onion sites, Syed speaks at tech conferences and contributes to open-source privacy projects. Syed’s expertise stems from hands-on testing of tools like Ahmia, NotEvil, and Haystak, coupled with a rigorous commitment to operational security. Use obfuscation tools like bridges, avoid patterns in searches, and layer with VPNs to reduce traceability, though nothing is 100% foolproof against sophisticated adversaries. While Tor provides strong anonymity, activity can potentially be traced through advanced techniques like timing attacks, exit node monitoring, or vulnerabilities in engine setups. Integrate with tools like dark web monitoring services for alerts on credentials or IP theft. Businesses can scan for leaked data or cyber threats using premium engines like Haystak for monitoring forums and marketplaces.



