Silk Road was one of the first dark web marketplaces that emerged in 2011 and has allowed for the trading of illegal drugs, weapons and identity fraud resources. Commercial darknet markets mediate transactions for illegal goods and typically use Bitcoin as payment. Thus, communication between darknet users is highly encrypted allowing users to talk, blog, and share files confidentially. Identities and locations of darknet users stay anonymous and cannot be tracked due to the layered encryption system. Tor browsers create encrypted entry points and pathways for the user, allowing their dark web searches and actions to be anonymous. The dark web has often been confused with the deep web, the parts of the web not indexed (searchable) by search engines.
Popular Reviews
If you’re planning your next vacation, a quality luggage set should be top priority. Ninja is on sale so often, it’s pretty much criminal to buy a new coffee maker at full price. If you’re a meal prepper and love the idea of home-cooked lunches for the office, this hidden Kohl’s sale is for you. Each year, Kohl’s always has some of the best (and most-searched-for!) deals to comb through before Black Friday. It’s Early Black Friday shopping time at Wayfair, where you’ll find up to 70% off furniture, outdoor pieces, decor and more.
For instance, he serves as a member of the National Security Telecommunications Advisory Committee (NSTAC), which advises the U.S. government on national security and emergency preparedness. Moreover, vast arrays of government agencies and non-governmental organizations as well as more than 400 million consumers rely on its cybersecurity solutions. Through his leadership, McAfee protects mission-critical systems and data for a myriad of the world’s largest publicly traded corporations. It handles such services for more than 7,000 organizations—including Microsoft, Macy’s, Netflix, and Intuit—in more than 120 countries. Phillips, who was named one of BE’s Most Powerful Executives in Corporate America has spent his career transforming companies with technology, industry domain, and unconstrained thinking. As CEO of one of the world’s largest providers of enterprise software applications since 2010, he has been responsible for doubling the company’s revenue to $2.7 billion and size to more than 15,000 employees.
Hacking Groups And Services
Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web. The dark web is filled with information theft from malware-infected users. Antimalware and antivirus protections are equally crucial to prevent malicious actors from exploiting you. Leaks of personal data can also lead to damage to your reputation via social fraud. Identity theft monitoring is critical if you want to keep your private information from being misused.
The spy agency is hoping to securely and anonymously collect tips, though its entire website, including job listings, are available on the onion service. The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. Hacker Lexicon is WIRED's explainer series that seeks to de-mystify the jargon of information security, surveillance and privacy.
Find The onion Address You Want To Access
Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service. On the dark web, "CP" most commonly stands for "Child Pornography." Engaging with or distributing such content is a serious criminal offense. It’s not illegal to visit the dark web in the United States.

Cybersecurity Threats
Besides demonstrating superior legal chops for the company that generated $4 billion in 2017 revenues, Taylor is a staunch advocate of corporate diversity, pushing for more black talent at Symantec and within the tech sector as a whole. At the time, he served as co-executive sponsor of Blacks at Microsoft and founding executive of BlackLight, an organization empowering black marketers at Microsoft. This innovator has also invested her time nurturing the careers of women and minorities both internally and externally.
- Real-time outage reporting curves provide instant tracking of interruptions and help identify spikes indicating major outages.
- He has also worked with software development and SaaS operations, mergers & acquisitions, and field technical sales.
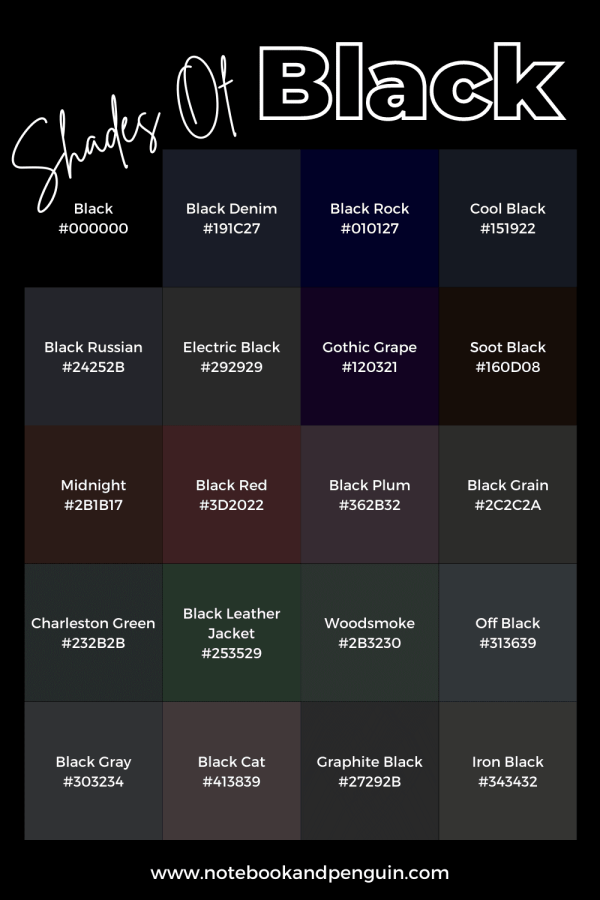
- The hidden nature of the dark web has earned it the nicknames black web and underground internet.
- However, the software that popularized the dark web is The Onion Router (Tor), which launched on September 20, 2002.
- Some were lawyers, some teachers, etc., all of whom were in this digital space, creating content, networking across the country and the world through new computing tools and devices and so forth.
Addresses also change frequently due to the transient nature of many dark web actors. Addresses tend to be a mix of random numbers and letters, making them challenging to remember or access manually. That said, it can be difficult for users to find the material they are looking for on the dark web. The most common of these browsers is Tor, which launched in 2002 and serves millions of users. The dark web offers both benefits and risks for users going into it, but the intent of the user will also impact this.

Forums and websites on the dark web are not moderated, so you can never be sure they are free from malware. Security solutions like anti-virus software protect your system and network from malware and other threats. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings. To access the dark web safely, you should enable strong security settings.
Websites and pages in the deep web might include password-protected content, private forums, and personalized resources. The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines. You could consider the clear or surface web the "top" and visible layer of the internet, easily accessible using a browser such as Safari, Chrome, Edge, or Firefox.
Black Business Directory
In 1989, Ian Clarke launched the Freenet project, which aimed to allow anonymous online interactions at a time when internet anonymity was difficult to achieve. Many of these services are legal and legitimate, but they can host illegal content or activity. There are many dark web search engines that can be used with Tor Browser, including Torch, Haystack, and Not Evil, to help you navigate to different sites and services. Normal sites on the deep net (like your online banking site or email account) sit behind secure logins, paywalls, passwords, and authentication forms, but you don’t need any special software to reach them. The key difference between the deep web and the dark web is that the deep web refers to all web content that requires login credentials to access, while you need special software to reach dark web content.
PRIVACY ALERT: Websites You Visit Can Find Out Who You Are
However, because it's almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. Take a look at the sites that these directories have collected and see what topics interest you.
Anonymity Is In Your Hands
"Understand that the web as we know it today is privacy-hostile and that nothing is foolproof, do research, support organisations and projects — like Tor Project, i2p, and Open Privacy — that are building and maintaining tools that make enforcing your consent easier." In short, even with Tor, there's no perfect anonymity online, but there are efforts to claw back our power online, says Lewis. There's no such thing as perfectly private or secure on the internet. "And if I use Tor then I have a good degree of certainty that at least the local weirdos are not looking over my digital shoulder at what I am browsing — and that when I kill my browser (unless I've bookmarked something, or saved a file) then all the data is properly cleaned-up and wiped."
URBAN NETWORK NEWS
Tor stands for "the onion routing project." It was developed by the U.S. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but "Tor is, by far and away, the most popular." Here's how that dark side of the internet actually works.
However, while Google alone has over 35 trillion web pages indexed from around the world, this only represents around 4% of the total internet that exists. To get you started, here are some amazing facts that you might not know about the Black Web/black Internet to help you get a rough idea when it comes to answering the question “what is the black web? You can find more of her work in various online pubs, including National Geographic, Insider, Kinkly, and others. She has a Master's degree in Creative Publishing and Critical Journalism from The New School of Social Research and is a grad of Sextech School.
Evans has also served as general manager of Wireless Platform Research & Development Group. Evans started her career at Intel in 2006, as a software integration and test manager. As Senior Vice President and Chief Strategy Officer at Intel Corp., Aicha S. Evans leads Intel’s efforts to convert from a PC-centric company to a data-centric juggernaut.
If you’re considering using the dark web for basic privacy purposes you might still question, “Is dark web dangerous to use? While it is not illegal as a whole, unsavory activity does live in many parts of the dark web. Ultimately, simply browsing these spaces is not illegal but can be an issue for you. If an activity is deemed illegal by the governing bodies you fall under, then it would be illegal. However, you can still take illegal actions within Tor that could incriminate you regardless of the browser’s legality. Some simply don't want government agencies or even Internet Service Providers (ISPs) to know what they're looking at online, while others have little choice.



