The dark web, or the darknet, is a small subset of the deep web. To look at it in a different way, it makes up between 90% and 95% of the internet. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word.
History Of Dark Web Marketplaces
- ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it.
- The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication.
- For additional security, users are advised to tumble or mix their coins through a trusted service before depositing funds into a market wallet, breaking the link between their clean coins and the market deposit address.
- The dark web is the World Wide Web content that exists on darknets (overlay networks) that use the Internet, but require specific software, configurations, or authorization to access.
- Its pseudonymous nature allows users to transact without directly linking their real-world identity to a purchase, a core requirement for secure operations.
- Silk Road was an online black market and the first modern darknet market.
Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. It allows users to stay safe from ISPs, governments, surveillance agencies, and hackers monitoring their activities, and is the perfect option to access the dark web. Please understand that engaging with platforms like darknet markets carries significant legal dangers. Therefore, you must know how to access dark web marketplaces safely (covered later in this article).
Legitimate Use Cases For The Average User
You could do all your browsing with Tor, though it's slower than a standard browser, something the Tor Project is working hard at to improve, says Stephanie Whited, communications director for the Tor Project. Once you've downloaded and installed the Tor browser, you can browse just as you would your usual browser, but Muffett offers a caveat to avoid unencrypted sites — those with only "http" in the URL rather than "HTTPS". Slide up to the "safest" level, and as well as those settings, JavaScript is disabled on all sites. In "safer" mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won't run automatically, you'll have to click to play.
Illegal Pornography
- We are committed to ensuring that our website is accessible to everyone.
- Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge.
- While detractors argue its use for activism invites political instability, proponents see it as a vital tool for transparency and dissent against oppressive regimes.
- Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal.
- Cyber crime and hacking services for financial institutions and banks have also been offered over the dark web.
To expand their reach, some marketplaces established parallel channels on Telegram. Regularly monitoring the top dark web markets gives your SOC team an insider’s view of the latest malware and phishing kit trends, plus real-time knowledge related to relevant compromised PII. Cybercriminals gather on dark web stores to buy and sell illegal goods and stolen data. Solutions like SAGA® by Munit.io help organizations gain visibility, detect emerging risks, and act quickly when their data, credentials, or brand appear in underground markets. Understanding how dark web marketplaces work helps analysts evaluate the extent of exposure during an investigation. Understanding how dark web marketplaces work helps organizations assess the risks they face.
For example, China uses the Great Firewall to block access to Western sites. You could be monitored closely even if you are not doing anything illegal. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Here are some of the common dark web dangers that users can face. All in all, it is not illegal to access the dark web, but it can create issues for you.
How To Download And Use Tor
Dark web marketplaces are infamous for being hotbeds of illegal activity, from selling malware and stolen data to offering all sorts of illicit services. Instead, users rely on dark web search engines like DuckDuckGo or directories, such as the Hidden Wiki and its offshoots, to find .onion websites. Tor browser and Tor-accessible sites are widely used among the darknet users and can be identified by the domain ".onion". The majority of users (over 90% as per our research) only need a Tor Browser for accessing .onion links; they don’t need to know about other methods.
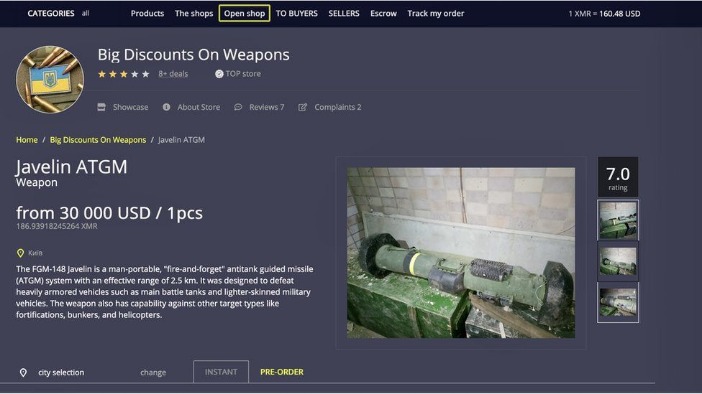
Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. Some dark web commerce sites have dangerous chemicals and weapons for sale. But there are also many illegal activities that happen on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. The Hidden Wiki is a surface website offering a collection of dark web links. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
Should I Only Use A VPN To Access The Dark Web?
Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Ransomware and cryptocurrency-based crimes saw a significant increase in 2025, with $2.17 billion stolen from crypto platforms, surpassing the total for all of 2024. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Dark Web Marketplaces continue to thrive as central hubs for these illicit transactions.
Hacking And Cybercrime Sites
This ecosystem represents a sophisticated alternative for procurement, characterized by its focus on accessibility and discrete logistics. The entire procurement journey, from initial search to finalizing a purchase with Bitcoin, is built upon the foundation of these reliable, updated pathways. The technical infrastructure supporting these transactions is robust, featuring automated payment tickers and real-time blockchain confirmations that streamline the purchasing process.

The Best Darknet Markets Of 2025 For Secure Shopping With Bitcoin
The feedback score provides a quantitative metric of reliability, calculated from the total number of successful transactions and positive reviews. Direct transfers from a personal, KYC-verified exchange wallet to a market escrow are considered a significant operational error, as it creates a permanent and easily traceable financial link. Bitcoin remains the foundational currency for darknet commerce, providing a necessary layer of financial separation between transacting parties. These systems provide a clear, crowd-sourced metric of reliability and product quality, significantly de-risking transactions for buyers.

Tor Network Architecture
It is a shared responsibility between market administrators and users, creating a resilient system where trade can flourish. This operational excellence ensures that users can shop with confidence, knowing the system is designed to facilitate secure and efficient transactions. Relying on outdated information leads to inaccessible links or, worse, exposure to phishing sites designed to steal user credentials and cryptocurrency. These lists act as a dynamic directory, cataloging the current status of platforms like Nexus Darknet, their operational mirrors, and verified onion links. Maintaining access to functional darknet markets requires consulting updated market lists from trusted community sources. Detailed product listings are a core function of any efficient darknet market, transforming a vast inventory into a navigable and user-friendly catalog.
Google Plans To Give Dark Web Monitoring To Everyone
By monitoring forums, marketplaces, and communication channels, security teams can identify emerging threats, compromised credentials, and chatter about planned attacks. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. In 2024, the platform grew significantly in popularity, partly because of its strategic acquisition of users from a number of recently shut-down marketplaces, such as AlphaBay and Incognito Market, which had recently closed their doors. Abacus Market offers an extensive array of illegal goods and services across various categories, making it one of the most versatile marketplaces on the dark web. Dark web marketplaces are hidden online platforms accessible through anonymizing tools such as Tor. This platform provides in-depth analysis, security guides, and educational materials about digital privacy, anonymous browsing, and darknet marketplaces.
The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. This is high-level protection; no one can intercept your data or activities. All the plans come with a 30-day money-back guarantee, so you can try the services risk-free. It offers multiple security protocols, including OpenVPN UDP/TCP, L2TP/IPSec, and PPTP.
The darknet markets of 2025 demonstrate significant advancements in operational security and user accessibility. For users, this translates into predictable and secure access to a global marketplace. Below is a structured catalog of darknet marketplaces, their onion links and mirrors. A high-quality darknet market now operates a vast network of mirrors, which are alternative .onion addresses that all lead to the same platform, ensuring that users are never locked out of their accounts or mid-transaction. The operational framework of leading darknet markets in 2025 mirrors that of surface web e-commerce platforms, creating a familiar and efficient environment for users.
Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands. Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data. Data breaches happen all the time, and your login credentials and other data might be on the dark web already.