The encrypted data is sent through a series of network-based nodes called onion routers. The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them. The Tor Browser (“The Onion Router”) is a product of the Tor Project, which was founded on the belief that “internet users should have private access to an uncensored web.” If you are reading this, you’ve likely heard about how the Tor Browser can help protect your internet privacy and anonymity online. A traffic correlation attack takes serious resources, but it’s doable for advanced actors with sufficient motivation. In rare cases, attackers can exploit an unsecure node to monitor Tor users or gain unauthorized access to accounts.
- RiseUp is a top dark web website that offers secure email services and a chat option.
- The dark web has several anonymity layers, making it difficult to access.
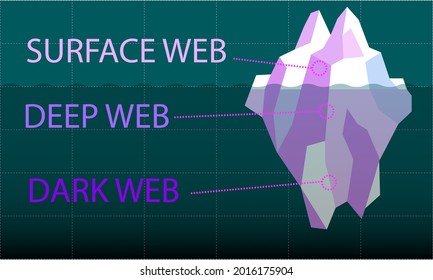
- The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose.
- Unlike Tor, I2P is designed for peer-to-peer services like file sharing, email, forums, and even decentralized websites — all within its own closed network.
- The installation on Linux involves extracting the contents of this archive to a directory of the user’s choice.
- This yields an exalted level of anonymity, rendering user activities nearly untraceable.
Is Accessing The Dark Web Legal?
- The quickest way to access the dark web is to download and install Tor Browser, which will route your traffic through the Tor network and let you access the dark web.
- Remember that no one can prevent all identity theft or cybercrime, and that LifeLock does not monitor all transactions at all businesses.
- Avoid altering any security settings in Tor that could reduce your protection.
- Here's everything you need to know about this other internet, as well as how to access it.
Like NordVPN, this provider doesn’t store logs and has around twenty third-party audits to prove it. Its affordable prices and unrelenting performance make NordVPN a standout option for dark web users. One of its key benefits is unlimited bandwidth, which allows for unlimited dark web browsing.
What To Do If You See Something Illegal
This article lists some of the best dark web websites you can visit securely. Despite the anonymity features of Tor Browser, users should also be aware of the potential for surveillance and tracking. While Tor Browser provides a degree of anonymity, accessing the dark web inherently involves exposure to a multitude of potential dangers.
How To Choose The Right Dark Web Monitoring Tools For Your Business?
A common inquiry from Tor users is if they should use a VPN to add an extra layer of protection. It encrypts data during transmission to avoid the risk of being eavesdropped. Tor doesn’t support plugins because they introduce security risks. Regular browsers can’t open Onion sites because they aren’t part of the standard domain name system. The above configurations help improve your security when surfing the web via Tor.
But it also contains other news and religious sites, private discussion forums, and medical records. You don’t need special tools or a special browser like you need to access the dark web (more about that later). That means that only 0.024% of all the known pages are findable in Google’s search engine.
What Are Dark Web Browsers?
Install Avast SecureLine VPN for Android to protect your privacy and keep your data from falling into the wrong hands. Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands. Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data. Data breaches happen all the time, and your login credentials and other data might be on the dark web already.
Is It Illegal To Use The Tor Browser?
It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Darknet markets facilitate transactions for illegal goods and services. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better.
How It Works: Tor Over VPN
Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. Many people install a VPN as well, but then you're putting your trust in an additional third party to not track your activities or report them to anyone else. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn't know exactly what you're doing. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they're doing and what they're looking for. Even with Tor and onion routing in place though, you're not suddenly completely invisible and free to do whatever you want, without repercussions.
How To Access Tor Via Tails OS On A USB Thumb Drive
Being hidden doesn't translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk. However, conducting criminal activities via the dark web is illegal. To access a dark web resource, you will need to know its web address to the letter. If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app. The Tor Browser uses several layers of encryption to strengthen your anonymity and has integrated the DuckDuckGo search engine, a system that makes a point of not saving or logging your search queries. You will need to visit the Tor Project to download the Tor Browser, a browser that prevents online fingerprinting, circumvents website blocks, and stops trackers from building a profile based on your browsing habits.
The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people). So, when measuring the total network of live dark web sites alongside the surface web, only about 0.005% of the internet is the dark web. Researchers from Recorded Future estimated that while there are more than 55,000 existing onion domains, only 8,400 (or roughly 15%) of these sites were active. The many layers of an onion represent the multiple layers of encryption in the Tor network.
Is Tor Safe?
These sites bypass copyright protection and may be accessed only on the Dark Web to avoid legal scrutiny. They often provide access to vast amounts of compromised data from previous hacks or breaches. Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information. However, not all the forums and social media sites are legal on the dark web and often include shocking conversations and pin boards by anonymous users. The dark web offers a marketplace section where users can buy legal or illegal products. Importantly, not all deep web content is illicit; much of it is benign and essential for everyday online activity.

The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.