NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to...
Uncategorized
It also states if any of these markets has active warnings.For the full chart, visitdarknet markets links....
His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance,...
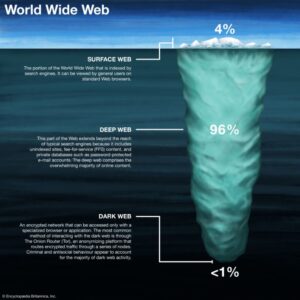
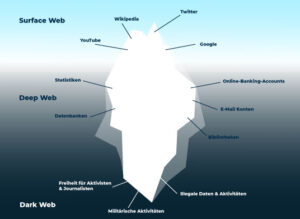
Unlike the surface web, it’s not indexed by traditional search engines, making it a haven for anonymity...
Established in 2012, the platform is a time capsule that collects snapshots of websites. While this is...
This website allows you to type in your email address or phone number and see if it’s...
Russian Market has been operating since 2019 and is one of the favorite destinations for those looking...
Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering...
Just like in the old days of the internet, the dark web maintains numerous indexes of sites,...
To access the dark web, you will need to use a special browser called the Tor browser....