In order to investigate the role of direct transactions between market participants, we now analyse the evolution of the S2S network, i.e., the network of the U2U transactions involving only sellers. Therefore, we analyse the temporal network where nodes are the active markets and an edge between the nodes represents the number of multibuyers between them, what we henceforth call the multibuyer network. In particular, multihomers that are sellers in multiple markets are multisellers, and similarly for buyers we have the multibuyers. To analyse the connectivity of the whole ecosystem, i.e., how markets are connected with each other, we consider sellers and buyers that are simultaneously active on multiple platforms. In fact, when we compute the total net income for each seller, a considerable fraction (16%) has a negative net income because they spend in markets where they are not classified as sellers, or in the U2U network.
Essentially, these payment processors provide a white label service for darknet markets and fraud shops, and a seamless checkout experience for those services’ customers. In recent years, some darknet markets and fraud shops have been integrating crypto payment processors on their websites via APIs, possibly as a way to improve operational efficiency and increase security. Since the takedown of Nemesis, Parsarad has discussed setting up a new darknet marketplace to take the place of Nemesis with vendors that were once active on the marketplace. Treasury remains focused on the risks posed by darknet marketplaces, as highlighted in previous designations of Genesis Market on April 5, 2023, and of Hydra Market on April 5, 2022. Identifying key players in dark web marketplaces through Bitcoin transaction networks. Since the beginning of DWMs’ activity, there has been a shift in the law enforcement approach from focusing on market admins towards sellers and buyers9,13.
Why Dark Web Monitoring Is Critical
Dark Web Marketplaces continue to thrive as central hubs for these illicit transactions. The underground data market's sophistication means organizations must assume their data is already compromised and focus on minimizing potential damage. The stolen data ecosystem has evolved into a sophisticated supply chain involving multiple players. Law enforcement warns that no site is safe previous markets even the biggest ones have all eventually fallen. Its fall disrupted a huge part of the global drug trade, showing that even sprawling, language specific markets can be dismantled.

What Is Cyber Threat Intelligence?
- Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay.
- Freshtools has some characteristics that help it stand out from the other dark web stores.
- As reported last year, some drug shops have been outsourcing services like website hosting and payment processing.
- Sixth, we consider the cumulative mean interevent time for each entity i at time t, defined as the mean of the sequence of time interval between consecutive transactions of an entity until time t, which we denote by \(\phi _i(t)\).
Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. The dark web is a part of the internet that isn’t indexed by search engines. Navigating the darknet requires vigilance. In 2025, it powers 2.5M+ daily users, with Germany leading in usage (followed by the U.S.). Tor Browser, built on Firefox, encrypts your traffic across 3+ relay nodes, enabling access to .onion sites. This guide provides verified .onion links, market stats, and expert insights into Tor and Monero usage as of February 21, 2025.
Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web. Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely. This step is independent of the sliding time window in step 2. To observe the behavior of the ecosystem on specific calendar periods, such as weekly or quarterly, we select a time period and aggregate the daily time series through step 3 accordingly.

Report Fraud, Waste & Abuse
The ASAP is a moderate design marketplace on the dark web that offers helpful tools like mandatory PGP encryption and two-factor authentication for a safe browsing experience. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. With a growing user base and expanding inventory, Vortex is positioning itself as an “all-in-one” darknet marketplace. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. Regardless of your jurisdiction, activities such as trading stolen financial data, compromised accounts, or money laundering services are illegal. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
- That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia.
- This guide explores the characteristics of darknets and dark markets, their implications for cybersecurity, and how they facilitate cybercrime.
- They are followed by market-U2U sellers, then market-only sellers, and lastly U2U-only sellers.
- Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there.
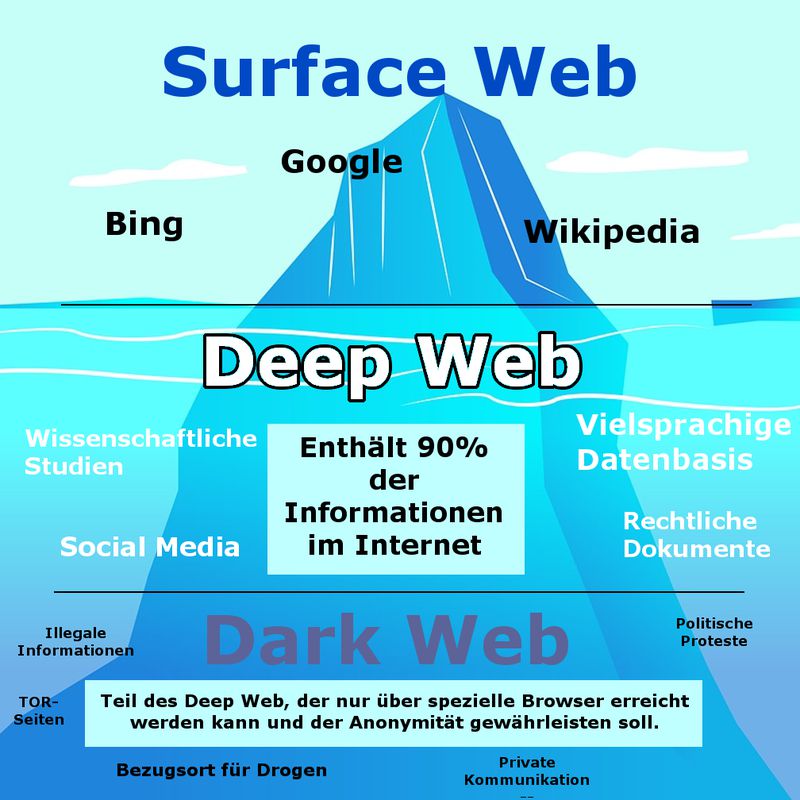
Are you struggling to stay on top of the main dark web markets worth monitoring? They use dark web search engines, specialized forums like Dread, and automation tools to monitor discussions for emerging threats and compromised data. Yes, the Hidden Wiki remains one of the most accessed community-curated directories for .onion links, though users must verify each link's authenticity. The Tor browser is a privacy-focused web browser that allows users to browse the internet anonymously, including accessing .onion domains on the dark web. The dark web is a hidden part of the internet that isn’t indexed by standard search engines and requires special tools like the Tor browser to access it.
You can legally browse darknet sites for legitimate purposes like research or privacy protection. The technology behind the darknet is actively maintained and continues to evolve. They operate similarly to regular e-commerce sites but use cryptocurrencies for transactions. You can access most deep web content through regular browsers with proper credentials.
Illicit Activity On The Dark Web
The structural change in the multiseller network and the resilience of the multibuyer network. This change persists until the end of the observed period of the data set (also see Supplementary Information S4). Then, between 2017 and 2018, there is a drastic structural change in the multiseller network structure due to operation Bayonet, after which the connections almost vanished.
📚 Contents
Though the drug transactions were limited to Russia and its geographic neighbors, the cyber and money laundering tools were available to anyone in the world willing to pay. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs. Individuals began using the darknet to pseudonymously sell illegal content without face-to-face interaction. In addition to content such as anti-authoritarian political sites within authoritarian regimes (e.g. citizens organizing protests during Arab Spring), the darknet is also a convenient place for illegal content such as DNMs, Child Sexual Abuse Material (“CSAM”), hacking forums, fraud forums, and money laundering forums. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed.
Dark Web Marketplaces

Others are looking for stolen data, hacking services, or even banned books and political content. To protect both parties, many marketplaces use an escrow system, so the money is only released to the seller once the buyer confirms that everything went smoothly. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
{Our analysts will continue to follow this market’s presence and reputation on the darknet, and provide further updates as this story unfolds. DarkOwl has assigned assets to monitoring and collecting data from the new AlphaBay Marketplace, leveraging our darknet intelligence capabilities, despite their increased crawler detection measures and ongoing server instability. ”} users comments were generally critical of the legitimacy of the marketplace, with comical references like “Welcome to the FBI HQ” posts. Dread staff “vouched” for DeSnake to skeptical darknet users with DeSnake signing documents using their historical PGP key. Operation Bayonet, which would ultimately lead to the shutdown of several prominent marketplaces, began with Dutch police seizing another lesser-known market called Hansa Market.|That same operation also shut down the dark markets DeepSea, Berlusconi, White House, and Dark Market. On April 28, investigations into the Italian Darknet Community (IDC) forum-based marketplace led to a number of key arrests. At the end of August, the leading marketplace Agora announced its imminent temporary closure after reporting suspicious activity on their server, suspecting some kind of deanonymization bug in Tor. On July 31, the Italian police in conjunction with Europol shut down the Italian language Babylon darknet market seizing 11,254 Bitcoin wallet addresses and 1 million euros. In April, TheRealDeal, the first open cyber-arms market for software exploits as well as drugs, launched to the interest of computer security experts. However Black Bank, which as of April 2015update captured 5% of the darknet market's listings, announced on May 18, 2015, its closure for "maintenance" before disappearing in a similar scam.|Later markets such as Evolution ban "child pornography, services related to murder/assassination/terrorism, prostitution, Ponzi schemes, and lotteries", but allow the wholesaling of credit card data. Personally identifying information, financial information like credit card and bank account information, and medical data from medical data breaches is bought and sold, mostly in darknet markets but also in other black markets. By 2015, some of the most popular vendors had their own dedicated online shops separate from the large marketplaces.|The evolution of the ecosystem of all buyers and sellers obtained from the considered markets and the U2U network is shown in Fig. We consider each market separately, i.e., we obtain a time series of buyers and sellers for each market, and we use the same method and classification parameters in the U2U network. Furthermore, we analyse the seller-to-seller (S2S) network, i.e., the network composed only of transactions among sellers, which can be regarded as a supply chain network of illicit goods and services. Specifically, we uncover distinct types of buyers and sellers based on their activity between markets and the U2U network, and detect a shift in the ecosystem’s activity towards the U2U network after a major external shock in the markets. Here, we set out to find the main actors in the DWM ecosystem and assess their systemic impact on a dataset of 40 million Bitcoin transactions involving the 31 major markets in the period 2011–2021.|Their presence can make you wonder why darknet markets and not just the regular online stores. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online. Not all marketplaces you want to visit can be accessed through regular search engines. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. Like other marketplaces, it also requires registration for new users and accepts payments in Monero.|In July 2017, the markets experienced their largest disruptions since Operation Onymous, when Operation Bayonet culminated in coordinated multinational seizures of both the Hansa and leading AlphaBay markets, sparking worldwide law enforcement investigations. From then on, through to 2016 there was a period of extended stability for the markets, until in April when the large Nucleus marketplace collapsed for unknown reasons, taking escrowed coins with it. The market owners set up a phishing website to get the attacker's password, and subsequently revealed collaboration between the attacker and the administrator of Mr Nice Guy's market who was also planning to scam his users. In March 2015, the Evolution marketplace performed an "exit scam", stealing escrowed bitcoins worth $12 million, half of the ecosystem's listing market share at that time.|Haystak is an advanced search engine for the dark web that offers a vast database of indexed .onion pages, helpful for professional intelligence collection. Trusted directories include Daniel’s Onion Directory, The Hidden Wiki, and TorLinks—all frequently updated with .onion links. Onion.live is a platform that tracks the status of dark web sites and provides trust ratings to help users verify site legitimacy.}
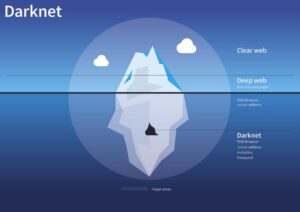
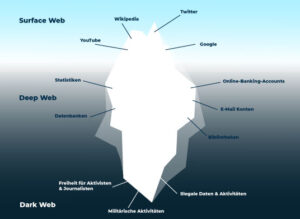
It consists of websites specifically designed to be anonymous and only accessible through special software like Tor. This deep web encompasses everything not indexed by search engines, including private databases, paywalled content, and, yes, the dark web. Imagine the internet as an iceberg. This shrouded corner of the internet can be both fascinating and dangerous, and understanding its workings is crucial in today’s digital age. The internet is a vast and ever-evolving landscape.
What Is Onionlive Used For?
For example, in some cases, a seller in a given market may behave as a buyer in a second market or in the U2U network. Third, at any given moment we classify entities as either buyers or sellers. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. These different regimes suggest that the ecosystem’s resilience is mainly supported by the high demand of buyers rather than the response of the sellers.
Fraud Shops Use Payment Processor To Boost Efficiency
Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
When a company discovers its data (credentials, PII, trade secrets) on the dark web, proactive response and legal compliance are essential. 🚨 Early detection on the dark web gives security teams a head start to rotate credentials, alert customers, and activate response plans before an attack escalates. From initial access brokers (IABs) to malware-as-a-service (MaaS) and negotiation platforms, nearly every stage of a ransomware attack has dark web fingerprints behind it. As cyberattacks and data breaches intensify in 2025, the volume of exposed credentials indexed on the dark web has reached unprecedented levels.