Leading platforms maintain multiple, geographically dispersed servers, automatically providing a new active URL should one become unavailable. The network's reliability and proven security record make it the preferred medium of exchange, supporting a stable economy for digital goods and services. This universality simplifies the process of acquiring goods, as vendors and buyers operate within a single, familiar monetary framework. The pseudonymity offered by the Bitcoin blockchain allows for a layer of financial privacy, though it is often enhanced through the use of mixing services and privacy-focused wallets.
But crucially, security is also a shared responsibility. Financial institutions must continue to innovate with stronger security measures like tokenization and advanced behavioral analytics. The sophisticated pricing structures and market dynamics demonstrate an industry that is resilient, adaptive, and highly organized. This is not a victimless crime; it fuels a global criminal network and imposes enormous costs on individuals, businesses, and the financial system as a whole. However, attackers are already adapting, focusing on compromising the online accounts linked to these wallets or using social engineering to trick victims into provisioning their cards to a criminal’s device.
Best Threat Intelligence Platform Vendors: Enterprise Buyer's Guide
- Yale Lodge’s website showing additions of cards from different US states.
- Beyond this, the selection includes digital products such as software, tutorials, and financial services.
- Top vendors establish reliable operational patterns, including predictable shipping times, consistent product purity, and professional customer service.
- Accessing these platforms requires a specialized browser, such as the Tor Browser, which is designed to connect to these onion addresses directly.
- For vendors, a stable market means predictable income and the ability to manage inventory effectively.
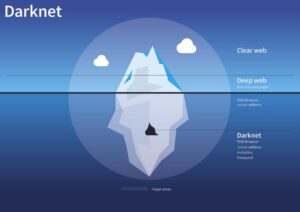
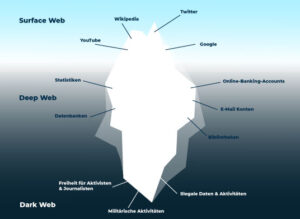
Silk Road’s demise proved that even Tor hidden sites could be penetrated by good detective work, prompting many users to flee to successor markets. These hidden markets promise anonymity, but in practice, users often slip up. These platforms facilitated the exchange of “CVVs” (a common term for card numbers with their security codes) and fostered a community where knowledge, tools, and data were traded. The proliferation of the internet and e-commerce in the late 1990s and early 2000s created the perfect storm for credit card fraud. This is the underground economy of the darknet, and its premier currency is the stolen credit card. To find these links, users rely on specialized darknet link directories and forums.

How The Darknet Enables Smooth And Secure Trade

Their specialty is selling stolen data, including login credentials, credit card information, and compromised accounts. It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. This marketplace focuses on selling stolen financial data, such as BINs (Bank Identification Numbers), RDP/VDS access, and verified crypto accounts for money laundering. These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access. A verified darknet market link serves as the primary defense against phishing attacks, which are designed to steal user credentials and cryptocurrency. This infrastructure supports a diverse marketplace where vendors can offer a wide array of products with a focus on transactional security and user privacy.
Beyond mere accessibility, these directories feature comprehensive vendor scorecards, which are compiled from verified buyer feedback. These lists function as a real-time dashboard, aggregating critical operational data that directly informs secure shopping decisions. This creates a fundamental layer of financial privacy for both buyers and vendors, which is a core requirement for these platforms.
Power Your Insights With Data You Can Trust
Financial institutions and security teams have developed pretty sophisticated detection methods that focus on behavioral patterns. When fraudulent transactions occur, merchants frequently end up eating the costs through chargebacks. Obviously, financial institutions bear the heaviest burden. Some threat actors even run automated validation services that check card numbers before the sale, guaranteeing their buyers a certain percentage of “live” cards.
Reliable Drug Stores With Fast Automated Service
This diversification is driven by vendor competition and consumer demand, leading to a more robust and specialized marketplace. This stability fosters greater trust within the ecosystem, encouraging a higher volume of commerce and attracting vendors with a proven track record. Early platforms were rudimentary and prone to exit scams, where operators would shut down the site and abscond with user funds.
The process begins with a vendor's shop, which functions as a dedicated storefront. Due to the nature of the darknet, the main URL can sometimes experience downtime. This specialized link is the primary gateway for all user interactions. Accessing the Nexus platform requires a precise approach to ensure a stable and secure connection. By reducing friction and building trust through design, these platforms foster a stable environment for trade.
Navigating The Best Darknet Markets Of 2025 For Secure Purchases
Market lists function as curated directories, presenting a comprehensive overview of available products and vendors. This transparent feedback loop ensures that vendors who provide high-quality products and reliable service gain prominence. Each vendor operates an independent storefront, with their organizational methods directly influencing sales volume and customer trust. This structured approach transforms the shopping experience into a streamlined process akin to using conventional e-commerce sites. Modern platforms function as comprehensive digital pharmacies, offering everything from classic plant-based products to sophisticated research chemicals and prescription medications.
Gaining reliable access to a major darknet market like Nexus is the foundational step for secure shopping, and the process has been refined to prioritize user safety and platform stability. Direct URLs are the primary mechanism for accessing darknet markets, functioning as the digital equivalent of a storefront address. The expansion of product categories on darknet markets represents a significant evolution in their operational model.
Why People Use Dark Web Marketplaces
A key feature contributing to this stability is the market's sophisticated system of mirror links and verified onion addresses. Modern platforms leverage optimized server infrastructure and load-balancing techniques to maintain uptime and handle high volumes of concurrent users without degradation in performance. Why credit card providers are opening lavish customer lounges in airports and cities. A letter posted on its homepage said it had been "a great pleasure to work with most vendors and users". In October 2021, White House Market – the largest darknet market of its kind – announced that it would shut down.
The combination of these technologies facilitates a secure environment for commerce. This mechanism distributes control, ensuring that no single party, including the market administrators, can unilaterally access the escrow funds. Furthermore, these platforms operate on a model of quality assurance and vendor accountability. The diversity of offerings demonstrates that these markets function as comprehensive, albeit illicit, commercial ecosystems. A legitimate Nexus URL will always be accompanied by a PGP public key\; users can verify the signature to confirm the link's authenticity before proceeding.
Common Types Of Data Bought & Sold:

Product listings are extensive and meticulously categorized, with vendor profiles displaying detailed feedback and transaction history. Palo Alto Networks Next-Generation security platform provides a holistic solution to protect the digital way of life by safely enabling applications and preventing known and unknown threats across the network, cloud and endpoints. It is imperative to have an understanding on how these criminals operate and the type of information being traded to better secure ourselves.

Digital Doppelgangers: Anatomy Of Evolving Impersonation Campaigns Distributing Gh0st RAT
- For enhanced security, privacy-focused cryptocurrencies like Monero (XMR) are increasingly accepted on platforms like Nexus.
- Once a legitimate link is acquired, users navigate to a user-friendly shop interface designed for streamlined and efficient trade.
- The currency's widespread adoption across all major darknet markets means users face no confusion when moving between platforms, creating a standardized economic environment.
- This focus on user experience minimizes errors and streamlines the entire purchasing journey.
- Transactions within this ecosystem are secured by advanced encryption protocols that protect all financial and personal data.
- Additionally, businesses can implement security measures such as encryption, firewalls, and two-factor authentication.
Access to the Nexus darknet shop is facilitated through its official .onion address, which is distributed through trusted channels and forums. This level of organization makes the darknet a practical source for a wide array of goods, meeting user demand with remarkable efficiency. This reliability directly contributes to the platform's operational stability and overall user satisfaction.
Top 7 Dark Web Marketplaces
The market server acts only as a relay, never possessing the decryption keys, thus ensuring that even platform administrators cannot access the contents of a private message or order detail. For the buyer, this translates to a reliable and predictable shopping environment where transactions can be completed with minimal delay, mirroring the convenience expected from surface e-commerce. Market lists and URLs are routinely updated to maintain functionality, ensuring continuous service for users seeking discreet procurement avenues. All websites hosting pornography will have to check the age of their users from Friday.