By signing up, you agree to the Terms of Use and Privacy Policy & to receive electronic communications from Vice Media Group, which may include marketing promotions, advertisements and sponsored content. The account requires an annual contract and will renew after one year to the regular list price. For any questions or doubts, either about the project or about us as research team, we remain active in this thread or through DM. Data obtained through this survey will also only be used for this research program, and will not be distributed to third parties. Recent years have seen quite some research into drug trade on the dark web. It added that many fraud shops are increasingly offering third-party crypto-payment processors like UAPS via API calls, as a way to reduce their own costs, improve operational efficiency and increase security.
The Full List Of Trusted Darknet Markets:
Freenet is similar to I2P – you can only connect to sites within Freenet’s own network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. In fact, I2P designed its own domain ending structure, called “eepsites.”
Mistake #3: Keeping Large Market Wallet Balances
The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control. Mega Market is known for its user-friendly interface and high security, including support for PGP encryption and two-factor authentication. The market is also known for its listings related to financial fraud, such as phishing tools and stolen credit card information. Dark web markets have gained notoriety for their illicit offerings.

Smart buyers compare pricing across multiple markets and vendors before purchasing. Lower-fee markets often offer better pricing, though other factors like vendor quality and selection matter equally. This decision guide helps match users with ideal markets based on individual requirements. Ordering and shipping is similar, but rather than adding funds to a marketplace wallet or account balance, the user pays the seller directly. It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers.
The Escrow Process
This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. If the product or service you’re attempting to buy is illegal, you’re running the risk of arrest. It’s no secret that the dark web can be a tricky and dangerous place for the general internet user. In darknet mode, you can select friends on the network and only connect and share dark web content with them.
For instance, you can choose the preferred security levels for enhanced protection. Changing the Tor browser settings can further boost your security levels on the dark web shops. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net.
- Threat actors and aspiring cybercriminals have been flocking to Telegram channels and groups hoping to benefit from even better anonymity and default end-to-end encryption.
- While it can be used for illegal activities, there are also perfectly legitimate forums, social networks, and communities.
- Not consenting or withdrawing consent, may adversely affect certain features and functions.
- What sets Abacus Market apart from other dark web platforms is its emphasis on customer service and their vendor verification system.
- Did you know that Google only shows you a glimpse of all the websites that actually exist?
- Then, users buy the products and the owners of the marketplace charge the sellers’ fees for using the service.
Search Darknet
What are the best markets? The ones that sell drugs, firearms, hacked Netflix accounts and all that. Honest feedback helps the community identify quality vendors and warn about problems.
This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Understanding what happens in these marketplaces is an important part of dark web monitoring. Cybercriminals gather on dark web stores to buy and sell illegal goods and stolen data.
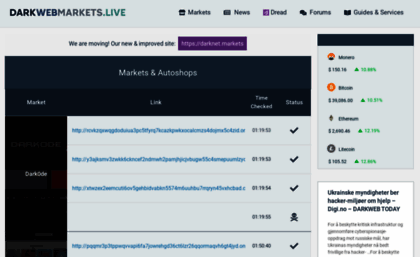
Placing orders on darknet marketplaces follows specific procedures ensuring security and successful delivery. Darknet marketplaces offer diverse product categories spanning physical goods, digital products, and services. Not all marketplaces you want to visit can be accessed through regular search engines.
KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. Using TAILS is yet another security measure that protects your online identity on the dark web.
Top Dark Web Market Shopping Guide 2026
However, I’ve come across many sketchy looking shops and marketplaces throughout my exploration, and I wanted to know “how legitimate” these sites are? Digital products include software, accounts, databases, tutorials, and various digital goods. Cannabis represents one of the largest categories on darknet marketplaces. Smart buyers compare options across vendors and even across markets.
HashJack Indirect Prompt Injection Weaponizes Websites
These alternatives aren’t necessarily safer or cleaner, they are merely alternatives for users wishing to keep their online activities as safe as possible. Obviously, since these websites don’t show up in the Google search engine, it can be a relatively hard task to find them. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Start the Tor browser by double-clicking on “Start Tor Browser” (for Windows) or “TorBrowser” (for Mac users). MacOS users will need to drag and drop the Tor Browser icon to the Applications folder.
Tor2Door Market
I actually ended up asking a friend who studied computer science to come over and help, as he had experience with the marketplaces. Although the safety data I collated and researched over so many years is now literally at the fingertips of countless thousands, this remains the case. In another unexpected turn, a growing number of individual vendors are also offering the PDF at point of sale.
Due to its absolute anonymity for knowledgeable users, the chance of running into bad people is also realistic, as they can operate relatively freely without the fear of getting caught doing something unlawful. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. In opennet mode, the network will automatically assign you to other users on Freenet’s network. I2P can only be used to access hidden sites that are only available on the I2P network.
Monero (XMR): Darknet’s Currency
After AB went offline I don’t which market is worth using. Create your account and connect with a world of communities. Long run with minimal issues, great security and competent support team.



