
Ahmia is one of the most respected dark web search engines available today. Remember to use the Tor Browser to access these, and always type the dotonion address carefully to avoid fakes. That’s why we’ve hand-picked twelve trusted .onion sites that continue to provide value, privacy, and reliability.
The keyword in that example is “onioname,” which is right at the start of the .onion link. OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. I also like that the security guides are user-friendly — the format is easy to scan, complicated terms are explained very well, and there are videos and screenshots.
Legitimate Use Cases For The Average User
This hidden content is primarily intended for privacy and security, catering to individuals, organizations, and services that wish to keep their activities private. This website used to host over 7,000 onion sites, giving users access to many dark web links. With DuckDuckGo, you can view dark web websites because, unlike regular search engines, it can index .onion websites. Unlike regular search engines such as Google, Yahoo, Bing, DuckDuckGo does not store your data, ensuring complete anonymity.
If you’re looking to understand how the dark web is shaping cyber threats in 2025–26, this comprehensive guide provides the stats, insights, and trends you need to stay informed—and stay secure. Whether you’re defending an enterprise environment or conducting digital forensics, data from the dark web is often the first sign of an incoming breach. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. Reflecting on the key dark web trends of 2023, it’s clear that the cybercriminal ecosystem on the deep and dark web is not just surviving but thriving, adapting rapidly to new technologies and global events. One possible explanation for this shift is possibly linked to the action law enforcement agencies have taken against dark web platforms, such as marketplaces. Another trend we’ve seen this year is that cybercriminals are now using chat applications, such as Telegram, more than other dark web platforms.
- Launched in March 2022 as a successor to RaidForums, BreachForums quickly became one of the leading forums for discussing data breaches and sharing stolen information.
- Their crawlers do not index .onion domains or any content on the Tor network.
- It’s crucial to employ a second level of security (a paid VPN) before you use the Tor browser.
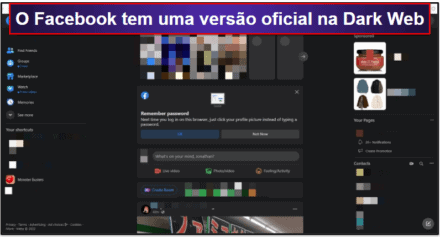
- Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer.
- You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
While a VPN adds valuable protection, being selective about which sites you visit and never sharing personal information are equally important. Your safety on the dark web depends more on cautious browsing habits than any single security tool. Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web. Cryptocurrency miners and other malicious software often target dark web users. This isolates any potential malware and prevents cross-contamination with your personal data. Create new anonymous accounts when necessary, using temporary email services.
What Is Spyware? Definition, Types And Protection 2026
These inputs are processed through AI pipelines that convert noise into meaningful indicators of compromise (IoCs). Machine learning predicts probabilities of data breaches, ransomware deployments, and insider leaks based on past campaigns. A single leaked credential on a darknet forum can cascade into supply-chain attacks or data breaches worth millions. It integrates natural language processing (NLP), graph analytics, and machine learning to uncover emerging threats, predict attack trends, and secure digital supply chains. In 2026, Dark Web Data Intelligence is a cornerstone of proactive cybersecurity.
Best Free Firewall Software In 2025
This .onion link makes it impossible for hackers to impersonate your profile. You only need to upload your PGP key or let the platform create one. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. That is why the explorers post their content on the dark web forums rather than the surface web. This .onion site is a bit different from the others reviewed above.
SmbCrawler – SMB Share Discovery And Secret-Hunting
- As long as you are not looking for anything illegal in the real world, it’s perfectly legitimate to use the dark web to find whatever you need.
- These platforms form the core of the most popular deepweb sites 2026, offering utility beyond the criminal narrative.
- Cybercrime services, such as hacking tools and stolen databases, are available for hire, creating a marketplace for illicit online activities.
- It strives to correct misconceptions and deliver precise scientific knowledge, making the intricate world of chemistry accessible and engaging to a broad audience.
- Riseup is not just another communication platform; it’s a movement.
Whether it's evaluating the effectiveness of marketing software or the security features of digital wallets, our reviews are a reliable resource for those in the know. Our meticulous reviews, based on hands – on experience, are designed to assist businesses in selecting the right tools for growth. In the online shopping space, we help retailers optimize their platforms and consumers find the best value. By closely monitoring market movements, we offer in – depth analysis that empowers businesses and individuals to make strategic decisions. Go-Beyond.biz is a trailblazing force in the digital business realm, specializing in online shopping, content creation and marketing, digital finance, and cryptocurrency.
Use A VPN Or Proxy For An Extra Layer Of Security
Avoid entering any real personal details or using existing accounts on dark web sites. NoScript and HTTPS Everywhere extensions provide additional protection against malicious scripts and unsecured connections. I always cross-reference links from multiple verified sources before visiting any dark web address.
These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. Everything you find on the dark web is not necessarily illegal. Not every visitor is a criminal, but this is where most cybercrimes begin. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.
Agentic AI–Driven Threat Intelligence Tailored For Every Function

DuckDuckGo is a search engine that prioritizes user privacy, distinguishing itself from competitors by not tracking search history or personal information. The Hidden Wiki categorizes links under several headings, making it easier for users to find what they're looking for. This assortment reflects the diversity of content available beyond the reach of standard internet browsing, including both legitimate resources and those of a more dubious nature.
Role Of Law Enforcement Agencies (LEAs)
To find .onion links for dark web sites, you’ll need to use a dark web search engine. Also, even in countries where accessing the dark web is legal, it’s still against the law to use or host sites that promote criminal activities. The deep web is made up of email platforms, workplace portals, subscription services, and banking websites — basically anything that requires a login. The dark web is a small part of the much larger “deep web,” which also isn’t indexed by search engines — but authorized users can access it using common web browsers. It’s made up of forums, marketplaces, and websites you can’t find with a Google search and requires specialized software to access, such as the Tor Browser. It lets you search both clearnet and dark web sites, but it blocks all trackers, doesn’t use your location data, and never stores your search history.

Top 10 Dark Web Search Engines In 2026 (Tools For Staying Anonymous On The Dark Web)
The challenge is that these legitimate sites exist alongside dangerous and illegal content. It allows citizens to access blocked news sites, social media platforms, and other information that their governments don’t want them to see. In an era of mass surveillance and data harvesting, some users simply want to reclaim their privacy and browse the internet without being tracked. The anonymity of the dark web unfortunately attracts a wide range of illegal activities. It has been intentionally hidden and requires special tools, like the Tor browser, to access. The deep web refers to any part of the internet that is not indexed by search engines.
Free The Internet
Especially as you are learning how to use the deep web, you will want to do this to avoid any of the more harmful phishing sites. You should rely on verified and curated scalar onion site lists from trusted sources. Additionally, you should not share any information to any sites that might cause you to be identified or linked to your name or other identifying information. You will also want to use a VPN, which will add another layer of protection and anonymity.
If you were a customer during the breach window but never received notice, you may still qualify—contact the settlement administrator directly. These states have genetic privacy laws with statutory damages provisions. If you lived in these four states during the breach period, you automatically qualify for a statutory payment of approximately $100—no proof of damages required. This makes genetic data breaches uniquely damaging and long-lasting.



