
Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection. Another challenge of finding dark web sites is that they don’t often last long. You can access all of these directories via the surface web.
- In March 2012 Russian hacker Yevgeniy Nikulin and three accomplices stole passwords for 117 million e-mail addresses from the social media company LinkedIn and then offered the data for sale on the dark web.
- The dark web is a hidden part of the internet that requires specific software, like the Tor browser, to access because it is not indexed by standard search engines.
- Dark web search engines are specialized tools that allow users to perform web searches within the dark and deep web.
- To properly peel back the internet's layers, you need a tool that provides layers of encryption to hide your activity.
- The first major Dark Web marketplace, used for drugs, fake IDs, and hacking tools.
Do Not Share Personal Information
Once you have accessed the dark web using the Tor Browser, finding specific sites can be challenging due to their complex URLs and the transient nature of many dark web pages. Content on the Dark Web exists on overlay networks that use the Internet and special tools and configurations to sustain security and privacy. The dark web hosts educational materials, whistleblower sites, and even mainstream media outlets, making it a valuable tool for research and information.
You can access it with regular web browsers and search engines. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Just like Google, the dark web has some search engines present on it. Although it’s no longer active, it’s setting the standard for coming onion links.
How Do I Get On The Dark Web?
The Hidden Wiki is a curated directory of .onion links that helps you find popular sites quickly. Most relays are openly accessible, but bridges stay hidden and are particularly useful in countries where access to the network is restricted or monitored. Search for lists of Tor hidden services–that is, lists of .onion sites–and you'll quickly see that most of them are either criminal or perhaps just downright repulsive.
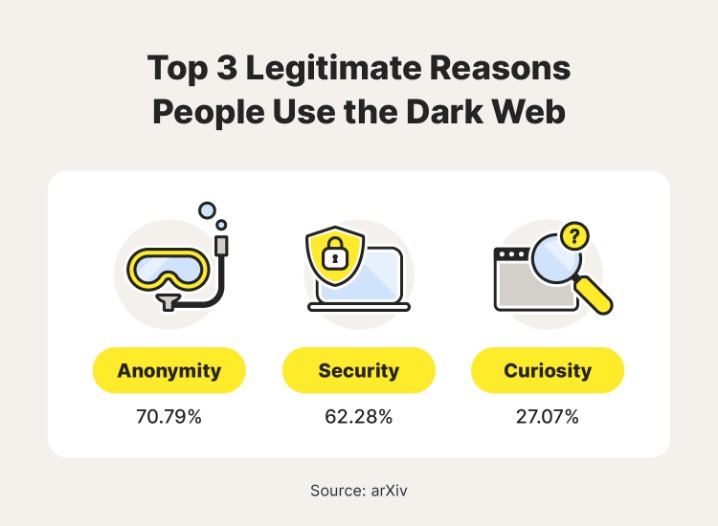
Privacy And Anonymity
The dark net is not quite as lucrative as it used to be and the prices for most of these items or services have gone down in recent years. Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023. That way, you can change your passwords and lock down your accounts to help block scammers from using your data against you. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data. Because of the dark web’s association with illicit activity, your use of Tor may be tracked by your ISP, drawing unwanted scrutiny to your browsing behavior.
Has Anyone Ever Been Arrested For Using The Dark Web?
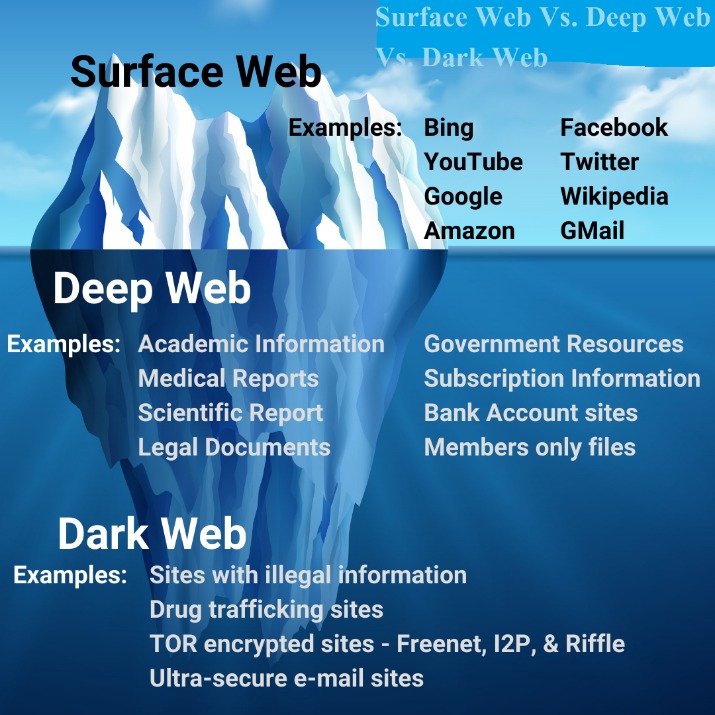
In this case either for technical reasons, or because the properties contain niche information that few people will want, or in some cases because the data is private. This scale is why newspapers and mainstream news outlets regularly trot out scare stories about ’90 percent of the internet’ consisting of the Dark Web. The Deep Web refers to all web pages that search engines cannot find. Our mission is to provide a reliable hub where individuals, businesses, and communities can access up-to-date information on a wide range of security topics. The dark web remains a mysterious part of the internet, offering both benefits and potential dangers.
Malware, ransomware, and hacking tools are also readily available for purchase or rent, enabling attackers to launch sophisticated campaigns. This layered encryption and anonymization make it difficult for authorities or outsiders to trace activities or identify participants. Some individuals turn to the dark web to protect their privacy and avoid surveillance, especially in countries with strict censorship or authoritarian regimes. These sites can be used by both hackers and individuals looking to exploit vulnerabilities.
Is It Illegal To Visit And Use Dark Websites?
Other anonymity networks such as I2P (Invisible Internet Project) and Freenet emerged, each offering different models for decentralized and private communication. These services laid the groundwork for what we now call the dark web. The concept of hidden networks began with early developments in anonymous communication technologies. By monitoring forums, marketplaces, and communication channels, security teams can identify emerging threats, compromised credentials, and chatter about planned attacks. Cybersecurity professionals can leverage the dark web for threat intelligence.
If your work or lifestyle requires you to use the dark web, however, there are ways to protect yourself. We put together a list of best practices you can use when exploring the dark web. But, of course, exercise caution and stay away from anything illegal. You’d also enjoy anonymity and privacy thanks to Tor’s encryption and routing, something you don’t get from most normal browsers. Despite all the dangers, there are actually advantages to using the dark web. We didn’t give them any information, but it’s scary to think how legitimate they sounded in the email.
Legitimate Use Cases For The Average User
Due to its anonymity, carding, fraud, and counterfeiting businesses are thriving on the dark web. For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users. The most prevalent dark web content is child pornography, about 80% of its web traffic, despite being challenging to find. Some fraudulent websites even pose as fronts for terrorist organizations like ISIL.
Instead, the dark web uses information from individual email or social media accounts, databases, and documents to give users access. The dark web presents various threats, including malicious software and computer viruses, posing risks to users' systems and data security. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.

However, if no one accesses data for a long time, it can disappear (this works much like BitTorrent, where files that aren’t actively seeded become de-indexed over time). A limitation of this system is that websites cannot be dynamic (so they’re always simple static HTML pages). However, on top of this basic file-hosting framework, volunteers have developed applications that allow for websites, message boards, and more. However, interest in I2P has waned badly in recent years (which itself impacts I2P’s security), so many I2P “eepsites” and forums are now abandoned.
Visit The Dark Web Websites Of Your Choice
For example, some services enable AI to bypass CAPTCHA systems, making it harder for sites to filter out legitimate traffic from abusive traffic. The operations are becoming more professional and many platforms mimic legitimate e-commerce sites displaying user reviews, seller ratings, and dispute resolution systems to build trust among illicit actors. “Churn is a major issue in attribution and tracking, and it’s often purposeful from threat actors who don’t want to get caught.” “Threat actors are wanting to drive focus on their own brand names to gain more notoriety for themselves, such as the regular launching of new ransomware group brand names and leak sites,” says Carroll. Popular malicious tools or services also include OTP bypass bots that automate voice or SMS to steal 2FA codes, crypto drainer kits that empty victims’ wallets, and deepfake services, according to Ian Ahl, SVP at P0 Labs. Ransomware leak sites showcase attackers’ successes, publishing sample files, threats of full data dumps as well as names and stolen data of victim organizations that refuse to pay.
These are pages and services that aren’t indexed by search engines, but they’re not hidden or secret — just restricted. The dark web is often used to bypass censorship and access restricted content in countries with heavy internet control, like China and Russia. “.Onion” sites are specifically designed to keep traffic and data private, which means they’re blocked from being found by regular search engines. It’s a solid starting point for exploring, but it’s important to read descriptions carefully — some links lead to illegal or dangerous content.
It is notorious for illegal transactions and activities such as drug trafficking, arms dealing and identity fraud. Beneath it lies the deep web and, further still, the dark web – a hidden network often shrouded in mystery, speculation and misinformation. We believe everyone should be able to explore the internet with privacy.We are the Tor Project, a 501(c)(3) US nonprofit.We advance human rights and defend your privacy online through free software and open networks. With Tor Browser, you are free to access sites your home network may have blocked. Meanwhile our company intranet is hidden from search engines, and requires a password.
The dark web is a hidden part of the internet not indexed by regular search engines, accessed through specialized browsers like Tor. Due to anonymity on the dark web, many consider it a place where online marketplaces for drugs, exchanges for stolen data, and other illegal activities occur. Several dark web search engines have been developed to index and provide access to hidden services. Unlike the surface web, which can be indexed by standard search engines, the dark web exists on encrypted networks and hosts websites with random, complex URLs.



